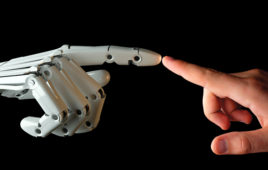
 Today’s automation connectivity support IIoT and Industry 4.0. setups, but the threat of cyber attacks on robots is very real. In fact, robots are just as exposed to corporate networks and the internet as other setups in industrial plants and applications — leaving them and their environments vulnerable.
Today’s automation connectivity support IIoT and Industry 4.0. setups, but the threat of cyber attacks on robots is very real. In fact, robots are just as exposed to corporate networks and the internet as other setups in industrial plants and applications — leaving them and their environments vulnerable.
Now a new report from Trend Micro details exactly how much of a threat cyber attacks on robots pose.
Trend Micro is a software company specializing in endpoint, server, and cloud security that sells Breach Detection and Intrusion Prevention Systems. The company offers what it calls a threat-intelligence network called the Trend Micro Smart Protection Network — software that continually uses data analytics and machine learning (as well as input from Trend Micro security experts and the Zero Day Initiative) for updates.
The white paper is called Rogue Robots: Testing the Limits of an Industrial Robot’s Security and details the ease with which industrial-grade robots are hackable.
Industrial robots are controlled and reprogrammable designs with multipurpose manipulators and programmable in three or more axes — either fixed in place or mobile — to serve industrial automation applications. One of the easiest ways to hack robots is through altering the industrial robot’s accuracy (without changing program code) to introduce minor defects into workpieces maliciously. These make for defective products and financial consequences as well.
The report details how a major entry point is though remote access and industrial routers — especially in mining, aerospace, automotive, and public-service industries.
The paper authors argue that industrial-robot standards must consider cybersecurity threats the same way ICS and automotive standards now do. Network defenders must comprehend how industrial robots work … and because robots have long lifecycles, vendors must work to provide regular security updates to all deployed variations. (In fact, the paper authors recognize the latter may be impossible in some .) In addition, end users must install software updates and and avoid makeshift patches — even if that temporarily causes downtime.
The white-paper PDF also lists actionable recommendations for boosting security of industrial-robot ecosystems. The researchers noted collaboration with ABB Robotics to investigate suggestions and begin a response plan on its current product line.
More technical details of the research (including vulnerabilities reported to vendors) will soon be released at the Institute of Electrical and Electronics Engineers (IEEE) Symposium on Security and Privacy in San Jose.
Another study by Trend Micro (and what it calls its Forward-Looking Threat Research Team) examined how critical infrastructure in the U.S. are most vulnerable because of the routers in networked applications being exposed as they are. Of course, a router’s purpose is make an Internet connection — but industry-level routers connect more sensitive resources than consumer-grade routers.
Cyber attacks on robots with concurrent reliance on industrial robots
Industrial robots have replaced manual labor in a lot of large-scale production. Robot efficiency, accuracy, and safety have boosted quality and throughput in the manufacture of cars, airplanes, food and beverage products, and even public utilities.
In fact, robots will soon become ubiquitous in modern plants … which begs the question: Is the current ecosystem of industrial robots secure enough to withstand cyber attack? This is the question the Forward-looking Threat Research team at Trend Micro and collaborators from the Politecnico di Milano (POLIMI) sought to answer. In fact, they demonstrate in the following video how easy it was to hack a working industrial robot. Architectural commonalities of today’s industrial robots (and strict standards) made the robot chosen for the studies representative of a large and common class of industrial robots.
Specific modes of cyber attacks on robots
Industrial robots usually rely on programmers or operators to setup high-level commands through a network … including remote-access interfaces such as teach pendants. Robot controllers then translate the commands into inputs for each joint or components of the robotic arm to execute. But the researchers identified five attack types possible once an attacker exploited the weaknesses of such industrial-robot architecture and implementation.
Software running on industrial robots is often outdated — based on operating systems and (in some cases) obsolete or cryptographic libraries. Elsewhere, software for robotics has weak authentication setups or even reliance on unchangeable credentials. Trend Micro even found tens of thousands industrial devices residing on public IP addresses — exposed industrial robots among them. The vendors, with whom we are working closely, have taken our results very responsibly, showing a positive attitude toward securing the current and future generation of industrial robots.

The first variation of cyber attacks on robots — altering control parameters
Here, the attacker alters the controls so the robot moves unexpectedly or inaccurately, at the attacker’s will. This can make for defective parts and degrade system safety and integrity.
The second variation of cyber attacks on robots — tampering with calibration parameters
Here, an attacker can change calibration settings to make the robot move unexpectedly. This can actually damage the robot and again — degrade system safety and integrity.
Here, there’s manipulation of robotic programs so that it outputs modified workpieces.
The fourth and fifth variations of cyber attacks on robots — altering plant-personnel signals on the robot
Here, an attacker either manipulates status information to mislead operators about the robot’s true status or manipulates the robot status itself. The danger here is injury to plant personnel.

Using these five modes of attack above, it’s possible to sabotage output workpieces with sometimes-invisible defects; install ransomware schemes to blackmail manufacturers for information on affected lots; damage robots and injure plant personnel that works near hacked robots; interfere with whole production lines through erratic robot-arm behavior that bottleneck operations; and (where robot controllers store source code and information about production schedules and volumes) extract sensitive data and industry secrets.




Tell Us What You Think!